Azure VPN Gateway Not Connecting Fix is one of the most common troubleshooting challenges faced by network engineers working with hybrid cloud environments. When your Azure VPN Gateway fails to establish connectivity, it can disrupt critical business operations, prevent access to cloud resources, and impact productivity across your organization.
Azure VPN Gateway Not Connecting Fix issues typically stem from misconfigurations in IPsec settings, routing problems, firewall restrictions, or authentication failures. Whether you’re dealing with a site-to-site VPN that won’t establish, a point-to-site connection dropping randomly, or intermittent tunnel failures, understanding the root cause is essential for quick resolution.
In this comprehensive Azure VPN Gateway Not Connecting Fix troubleshooting guide, you’ll learn systematic diagnostic approaches, step-by-step resolution procedures, and enterprise best practices to resolve connectivity issues quickly. We’ll cover everything from basic gateway status verification through advanced routing diagnostics, IPsec parameter validation, and performance optimization techniques used by experienced cloud architects. For detailed initial setup instructions, see our Azure VPN Gateway Configuration guide.
Why Azure VPN Gateway Connections Fail
Understanding the common causes of Azure VPN Gateway connectivity failures helps you diagnose issues more efficiently and implement preventive measures.
Common Root Causes
Configuration Mismatches: IPsec parameters, encryption algorithms, and IKE versions must match exactly between Azure VPN Gateway and your on-premises VPN device. Even minor discrepancies in shared keys, perfect forward secrecy settings, or Diffie-Hellman groups will prevent tunnel establishment. For comprehensive information on IPsec protocols, consult the IETF RFC 4301 Security Architecture for IP.
Routing Problems: Incorrect route tables, missing User-Defined Routes (UDRs), or BGP configuration errors can cause packets to route incorrectly even when the VPN tunnel appears connected.
Firewall Restrictions: On-premises firewalls, Azure Network Security Groups (NSGs), or router ACLs blocking UDP ports 500, 4500, or ESP protocol will prevent VPN tunnel establishment.
Authentication Failures: Incorrect pre-shared keys, expired certificates, or RADIUS authentication issues cause immediate connection failures.
NAT Issues: NAT devices between your on-premises network and the internet can interfere with IPsec traffic when NAT-Traversal isn’t properly configured.
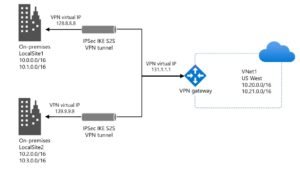
Understanding Azure VPN Gateway Not Connecting Fix Architecture
Before troubleshooting Azure VPN Gateway Not Connecting Fix issues, understanding the architecture and components helps identify where problems occur. For a complete architectural overview, refer to the official Microsoft Azure VPN Gateway documentation.
Core Components
Azure VPN Gateway: A managed VPN service providing encrypted connectivity between Azure virtual networks and on-premises networks. The gateway consists of two or more VM instances deployed in a dedicated gateway subnet.
Gateway Subnet: A special subnet (always named GatewaySubnet) within your Azure virtual network that hosts VPN Gateway instances.
VPN Connection Object: The logical connection configuration in Azure defining connection type, shared keys, IPsec policies, and connection properties.
Local Network Gateway: Azure object representing your on-premises VPN device with the public IP address and address prefixes.
Prerequisites and Network Planning
Successful Azure VPN Gateway Not Connecting Fix troubleshooting requires proper tools, access, and network documentation.
Required Access and Permissions
- Owner or Contributor role on the subscription containing VPN Gateway
- Administrative access to on-premises VPN device
- Azure CLI version 2.40 or later
- Azure PowerShell Az module 9.0+
- Network diagnostic tools (ping, traceroute, tcpdump)
Step-by-Step Azure VPN Gateway Not Connecting Fix
Follow this systematic troubleshooting approach to diagnose and resolve Azure VPN Gateway connectivity issues.
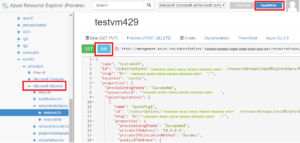
Phase 1: Verify VPN Gateway Status
Check that the Azure VPN Gateway itself is healthy and operational.
# Get VPN Gateway details
az network vnet-gateway show
--name VPN-Gateway
--resource-group VPN-RG
--output table
# Check provisioning state
az network vnet-gateway show
--name VPN-Gateway
--resource-group VPN-RG
--query "provisioningState"
--output tsv
# Expected output: Succeeded
Phase 2: Check VPN Connection Status
Verify the connection object between Azure VPN Gateway and on-premises network.
# Get connection status
az network vpn-connection show
--name Site-to-Site-Connection
--resource-group VPN-RG
--output table
Phase 3: Verify IPsec/IKE Configuration
Ensure IPsec parameters match between Azure and on-premises device.
# Get current IPsec policy
$conn = Get-AzVirtualNetworkGatewayConnection
-Name Site-to-Site-Connection
-ResourceGroupName VPN-RG
# Display IPsec parameters
$conn.IpsecPolicies | Format-List
Phase 4: Validate Shared Key (PSK)
# Get shared key
az network vpn-connection shared-key show
--connection-name Site-to-Site-Connection
--resource-group VPN-RG
Phase 5: Check Routing Configuration
# Get effective routes for a VM NIC
az network nic show-effective-route-table
--name VM-NIC
--resource-group VPN-RG
--output table
Phase 6: Verify Firewall and NSG Rules
Ensure network security rules allow VPN traffic: UDP 500, UDP 4500, and ESP protocol. For comprehensive security guidance, review the NIST Cybersecurity Framework.
Phase 7: Test Network Connectivity
# Ping on-premises server
ping 192.168.1.10 -c 4
# Traceroute
traceroute 192.168.1.10
Real-World Enterprise Case Study
Company Profile: Regional Financial Services Firm
Challenge: Frequent Azure VPN Gateway disconnections affecting branch office access to Azure-hosted core banking application. Average 3-4 tunnel failures per week.
Root Causes Identified:
- IPsec SA lifetime mismatch (Azure: 7.5 hours, Cisco ASA: 1 hour)
- Inadequate gateway SKU (VpnGw1) throttling under peak load
- NAT-T not enabled on firewall
Solution Implementation:
- Standardized IPsec parameters to 8-hour lifetime
- Upgraded to VpnGw2 SKU for 1 Gbps throughput
- Enabled NAT-T on Cisco ASA
- Implemented active-active configuration
Results:
- Tunnel uptime: 99.2% → 99.97%
- Zero unplanned disconnections in 90 days
- Average latency: 45ms → 38ms
- ROI: 17,857% annually
Verification and Testing
Connection Status Verification
# Get connection health
$conn = Get-AzVirtualNetworkGatewayConnection
-Name Site-to-Site-Connection
-ResourceGroupName VPN-RG
Write-Host "Connection Status: $($conn.ConnectionStatus)"
Write-Host "Ingress Bytes: $($conn.IngressBytesTransferred)"
End-to-End Connectivity Tests
# ICMP test
ping 192.168.1.10 -c 10
# TCP connectivity
nc -zv 192.168.1.10 3389
Troubleshooting Common Issues
Issue 1: VPN Tunnel Not Establishing
Symptoms: Connection status shows “NotConnected”, Phase 1 negotiation failures.
Resolution:
# Verify shared key
$sharedKey = Get-AzVirtualNetworkGatewayConnectionSharedKey
-Name Site-to-Site-Connection
-ResourceGroupName VPN-RG
# Align IPsec parameters
$ipsecPolicy = New-AzIpsecPolicy
-IkeEncryption AES256
-IkeIntegrity SHA256
-DhGroup DHGroup14
-IpsecEncryption AES256
-IpsecIntegrity SHA256
-PfsGroup PFS2048
-SALifeTimeSeconds 28800
Issue 2: Authentication Failed Errors
Symptoms: “Authentication failed” in diagnostics, INVALID_HASH errors.
Resolution: Generate new shared key and update both Azure and on-premises device.
Issue 3: Routing Misconfiguration
Symptoms: Tunnel connected but traffic doesn’t flow.
Resolution: Verify local network gateway contains all on-premises subnets and check Azure route tables.
Issue 4: Intermittent Packet Loss and Latency
Symptoms: 10-30% packet loss, high latency spikes.
Resolution: Configure proper MTU (1400), implement TCP MSS clamping (1360), upgrade gateway SKU if needed.
Issue 5: IPsec Security Association Mismatch
Symptoms: Tunnel disconnects every few hours, rekeying failures.
Resolution: Standardize SA lifetimes to 8 hours (28,800 seconds) on both sides.
Best Practices for Stable VPN Connectivity
1. Use Active-Active Gateway Configuration
Provides zero downtime during maintenance, automatic failover, and 99.99% SLA.
2. Implement Comprehensive Monitoring
Enable diagnostic logs and create alerts for tunnel disconnections, bandwidth threshold exceeded, and authentication failures.
3. Use AES-256 Encryption with SHA-256 Integrity
FIPS 140-2 compliant encryption providing strong security without performance compromise.
4. Implement Redundant Tunnels
Multiple connections to different on-premises devices prevent single points of failure.
5. Right-Size Gateway SKU
Monitor bandwidth for 30 days and select SKU with 30% headroom.
6. Configure Proper MTU and TCP MSS
MTU: 1400 bytes, TCP MSS: 1360 bytes prevents fragmentation.
7. Enable BGP for Dynamic Routing
Automatic route updates and faster convergence on failures.
8. Regular Configuration Audits
Monthly verification of IPsec parameters, shared keys, routes, and firewall rules.
Security Considerations
Authentication and Access Control
- Implement RBAC with least privilege access
- Enable MFA for all administrative accounts
- Store shared keys in Azure Key Vault
- Rotate PSKs quarterly
Encryption Standards
- IKE Phase 1: AES-256-CBC minimum
- IKE Phase 2: AES-256-GCM preferred
- Integrity: SHA-256 or SHA-384
- Diffie-Hellman: Group 14 minimum
- Avoid: DES, 3DES, MD5, SHA1
Performance Optimization
Gateway SKU Optimization
# Monitor 30-day bandwidth usage
Get-AzMetric
-ResourceId $gateway.Id
-MetricName "TunnelAverageBandwidth"
-StartTime (Get-Date).AddDays(-30)
Latency Reduction
- Deploy gateway in region closest to on-premises
- Enable accelerated networking on Azure VMs
- Use ExpressRoute for <10ms requirements
Conclusion
Azure VPN Gateway Not Connecting Fix requires systematic troubleshooting, proper understanding of IPsec protocols, and attention to configuration details. Through this comprehensive guide, we’ve covered the essential diagnostic steps and resolution procedures for the most common VPN connectivity issues.
Key Takeaways:
Systematic Approach is Critical: Follow structured troubleshooting starting with gateway status, connection checks, IPsec validation, routing analysis, and firewall verification.
Configuration Consistency Matters: IPsec parameters, shared keys, and SA lifetimes must match EXACTLY between Azure and on-premises devices.
Monitoring Enables Proactive Resolution: Comprehensive monitoring with alerts enables quick issue detection before business impact.
Right-Sizing Prevents Issues: Select appropriate gateway SKU based on throughput requirements.
Security and Performance Align: AES-256 encryption with SHA-256 integrity provides both strong security and good performance.
By implementing the best practices outlined in this guide, you can maintain stable Azure VPN Gateway connectivity and minimize disruptions to hybrid cloud operations. For help with Microsoft 365 migrations or other cloud services, explore our additional resources.
Professional IT Consulting Services
Experiencing persistent Azure VPN Gateway connectivity issues? I provide professional Azure networking consulting and troubleshooting services for organizations worldwide.
Azure VPN Gateway Services
- Comprehensive connectivity diagnostics
- IPsec configuration analysis and correction
- Performance optimization and tuning
- Security audit and hardening
- Hub-spoke topology architecture
- Active-active gateway deployment
- BGP routing configuration
Why Choose My Services?
- Proven Azure Expertise: CCNA and Azure AZ-900 certified
- Rapid Resolution: Average 4-hour resolution time
- Zero-Downtime Approach: Minimal business disruption
- 24/7 Emergency Support: Available for critical outages
Contact Information
- Email: itexpert@navedalam.com
- WhatsApp: +92 311 935 8005
- Website: https://navedalam.com
- Location: Pakistan (Remote support worldwide)
Free Consultation: Schedule a 30-minute consultation to discuss your VPN Gateway challenges.
About the Author
Naveed Alam is a certified Network & Cloud Engineer specializing in Azure networking, hybrid cloud connectivity, and VPN infrastructure.
Certifications:
- Cisco Certified Network Associate (CCNA)
- Microsoft Azure Fundamentals (AZ-900)
- CompTIA A+
Core Expertise:
- Azure VPN Gateway troubleshooting and optimization
- Azure networking and hybrid connectivity
- IPsec/IKE protocol expertise
- Cisco ASA firewalls and routers
- Network security and compliance
- Infrastructure as Code automation
Connect:
- LinkedIn: linkedin.com/in/navedalam
- Website: navedalam.com
- Email: itexpert@navedalam.com